Analysing CyberSecurity Jobs
SOC As a Security Operations Center (SOC) Analyst, you would have the following responsibilities and characteristics: In this role, you would be at the forefront of protecting an organization’s IT…
SOC As a Security Operations Center (SOC) Analyst, you would have the following responsibilities and characteristics: In this role, you would be at the forefront of protecting an organization’s IT…
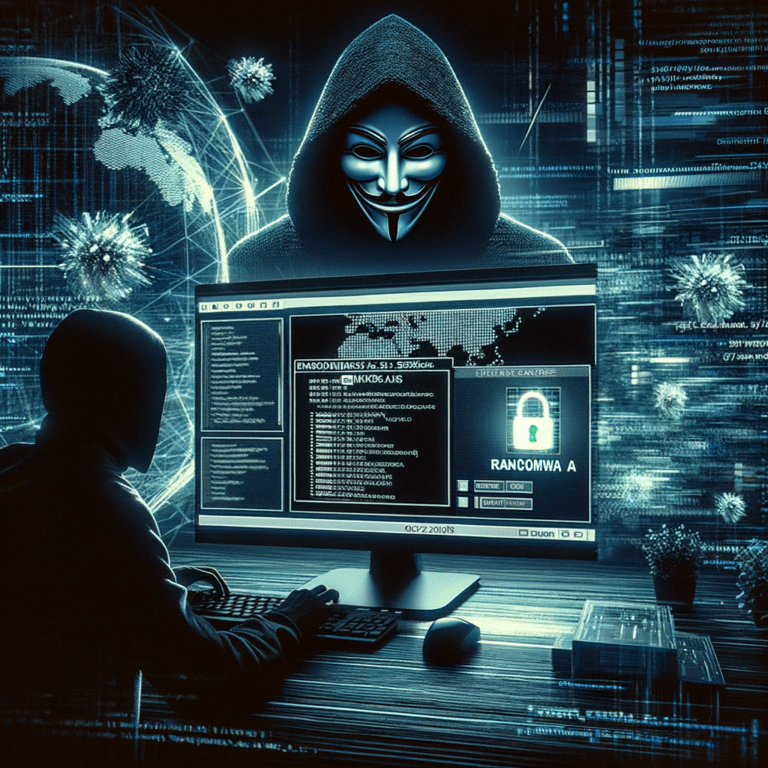
Introduction In the dynamic world of cyber threats, Ransomware as a Service (RaaS) has emerged as a formidable challenge. This model, resembling legitimate software-as-a-service offerings, enables even those with minimal…
Introduction Embarking on a cybersecurity career? Your success could hinge on mastering the right programming languages. This blog dives into why specific languages are critical for different cybersecurity roles. Python:…
Introduction Having a cybersecurity career is exciting, but the journey is fraught with potential missteps. This blog outlines common mistakes to avoid, ensuring a smoother path to your dream job…
The speed and agility of DevOps delivers tremendous business benefits. But that velocity can also introduce vulnerabilities without controls in place. Here we explore how organizations can embed security into…

The healthcare industry is under siege from cyber threats, as evidenced by the recent Welltok data breach. This incident exposed the personal data of a staggering 8.5 million patients in…
In a surprising turn of events, OpenAI announced early Wednesday that Sam Altman would reinstate his CEO role. This decision revealed on the social media platform X (formerly known as…

In the dynamic world of digital identity and security, OpenPubkey stands out as a groundbreaking security protocol. It innovatively enhances OpenID Connect by integrating user-held signing keys, transforming how ID…
In the digital age, privacy and anonymity are more than just buzzwords; they are essential components of our online freedom. The Tor network has been a bastion of these principles,…
Introduction: In the fast-changing world of cybersecurity, staying updated on the latest threats is vital. One recent development that’s raised red flags in the cybersecurity community is the emergence of…